10 Things You Should Do to Ensure Physical Cybersecurity
Its not just Santa coming through your chimney this holiday season If youre not careful unwanted guests may look to enter as well taking physical...

It’s not just Santa coming through your chimney this holiday season. If you’re not careful, unwanted guests may look to enter as well, taking physical steps to compromise your data. Your physical cybersecurity efforts should be designed to withstand these threats.
No, that probably doesn’t mean you need to block up the chimney and risk losing out on gifts. It does mean taking preparatory steps. These 10 things help you ensure physical cybersecurity, minimizing the risk of data breaches both through your servers and in-person actions.
1) Protection Against Dumpster Diving
What if stealing wasn’t illegal? That, in essence, is what dumpster diving comes down to. It’s one of the few completely legal ways in which others can steal sensitive information if you’re not careful. The legality and relative ease of it make it inherently dangerous.
To protect against it, you can start by making sure that nobody can walk into your building and simply steal your garbage. Ensure that all important documents are shredded, and still remain secure. If you use a remote shredding service, make sure they have chain of custody controls in place that allow you to track ownership of the sensitive document at any point.
 2) Site Access Control
2) Site Access Control
Do you know who can actually access your premises? Especially in an area where sensitive data is handled and stored, that becomes a crucial question. Lack of access control can be devastating if the wrong person gets in and gets access to your data. Fortunately, a number of modern tools help you optimize your access control. Open Path is a mobile system that allows access to specific people within the directory using smartphones and other devices. Another example is Envoy, which allows you to expand access to guests on a controlled basis.
3) Employee Awareness Training
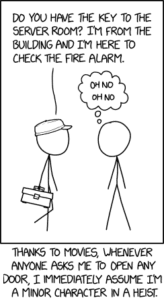
Negligent employees are the number one cause of cybersecurity breaches. That doesn’t come out of malice. More likely than not, your teams simply don’t know the importance of physical cybersecurity or the steps they should take to keep the company secure.
Employee awareness trainings can help. That starts with accountability; when someone sees something suspicious, encourage them to speak up. Ask yourself: could a guy with a clipboard walk through your office and take notes, without knowing anyone, yet avoid getting questioned? Your employee awareness training should focus on one underlying theme: avoid the SEP field.
 Fingerprint scanning on a smartphone screen, biometric cybersecurity scanner
Fingerprint scanning on a smartphone screen, biometric cybersecurity scanner
1) Secure Network-Enabled Printers
Network printers are convenient. They allow anyone in the office to get connected, without the need of extra wiring. Unfortunately, they are also a security risk. Many of them, through default settings, offer open wifi access, allowing anyone to get in and open vulnerabilities in the process.
We’ll guess that you probably don’t want your printer hacked by a phone on a drone. To prevent that from happening, inventory your network devices and only connect those to the internet that actually need to be. If only people in your office use the printer, remote access will not be necessary. Adding passwords to the connection can also help.
1) Building Secure Guest WiFi
When you have guests or visitors, they probably want the internet. Guest WiFi is a natural solution. Of course, it also allows external users access to your network, which they can exploit to sometimes devastating consequences.
Again, a few tips can prevent that threat. Segment your networks, which isolates Guest WiFi from your internal devices and data. Change the default passwords of all devices on the network, and encrypt your wireless signals. Through this type of segmentation, your visitors can safely enjoy the internet without presenting a potential problem.
6) Securing Your Windows
Physical cybersecurity can be as simple as a walk through the premises. Everyone loves an office with a window. But what if someone can actually use that window to find and exploit your data? Naturally, you want to avoid that potential exploitation. If you hold data that hackers would love to get their hands on, they’ll try any method - and might just look through the window. Make sure you know the sight angles to position your screens and other devices. That way, you can easily protect your team from onlookers looking to surf passwords and collect sensitive information.
7) Accounting for Lost or Stolen Devices
As devices become more mobile, the potential for them being stolen or simply falling out of someone’s pocket becomes more frequent. Of course, you don’t want your employee to leave their laptop behind on a subway train. But when the inevitable human error kicks in, do you have a contingency plan?
Mobile Device Management can help you take some of those preparations. The right platform allows you to lock down, and potentially swipe any lost or stolen devices from your organization remotely. Even if no one actually takes it, you’re still protected just in case.
8) Locking Up Your Servers
Obvious? Maybe. That doesn’t make it any less crucial. Any area in your business that stores actual data needs to be secured. That means locking office doors, and making sure that any server area gets extra protection. That way, you avoid the risk of anyone simply walking in, taking the storage containers, and walking back out.
9) Implementing Video Systems
For more secure premises, a video surveillance system may be a better solution. Yes, simply locking doors and server areas can help. Don’t end there. To make sure you know what’s going on, a video system can do wonders.
First, the mere presence of cameras can deter potential hackers. Second, the availability of video footage allows for a constant overview over the entire premises. Third, should something happen, you can easily reconcile the process, secure it, and catch the perpetrator.
10) Securing Your Backups
Finally, consider the importance of data backups for your business. Physical backups are an important part of business continuity, helping you prevent data loss in the face of outages, disasters, and more. But they also introduce potential vulnerabilities. Too many businesses secure their servers but forget about the backup devices. And yet, they store the exact same data. If someone can steal them, watch out. Treat them just as you would treat your most sensitive information, because that’s exactly what’s stored on them.
Start the New Year With Better Physical Cybersecurity Efforts
A week away from the new year, it’s time to start thinking about the ways in which you can protect your company and its sensitive data. Yes, that means better cybersecurity software systems, firewalls, and more. It also means understanding the physical implications.
Comprehensive physical cybersecurity has to be holistic, considering every possible way someone could get to your data. To get started in these efforts, contact us. We’d love to work with you in the new year to ensure better, more secure business operations.





